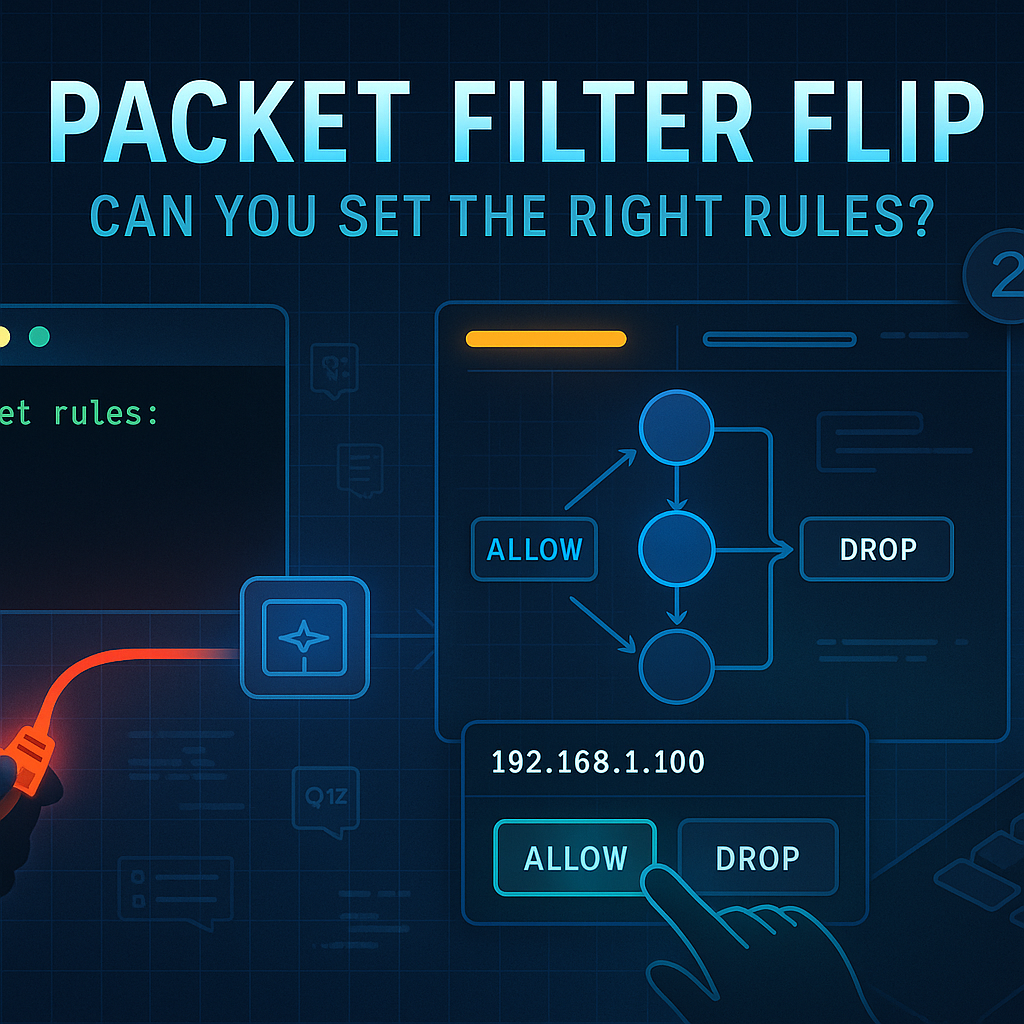
🧱 Packet Filter Flip: Can You Set the Right Rules?
Can you configure a packet filter under pressure? Flip the correct ALLOW/DROP flags in this…
🕷️ Interactive Threat Honeypot Designer: Build, Simulate & Visualize Cyber Deception
Visually build and simulate deceptive honeypot networks with real-time threat triggers, port/service config, and persistent…
🛠️ HTTP Header Builder Challenge: Can You Construct These Requests?
🛠️ Test your HTTP knowledge with this puzzle! Drag and drop the correct headers to…
Entropy Visualizer & Simulator – Interactive Entropy Heatmap for Randomness Testing
Visualize and simulate cryptographic entropy in real-time with animated graphs, heatmaps, and input simulators—fully client-side…
Escape the Logs 🧩: A Log Analysis Puzzle Game for IT Pros
Escape the Logs is an interactive troubleshooting game where you test your ability to find…
🧬 Malware Behavior Visualizer — Interactive SVG Security Simulation Tool
Simulate and visualize how malware like worms, trojans, and ransomware spread across systems using a…
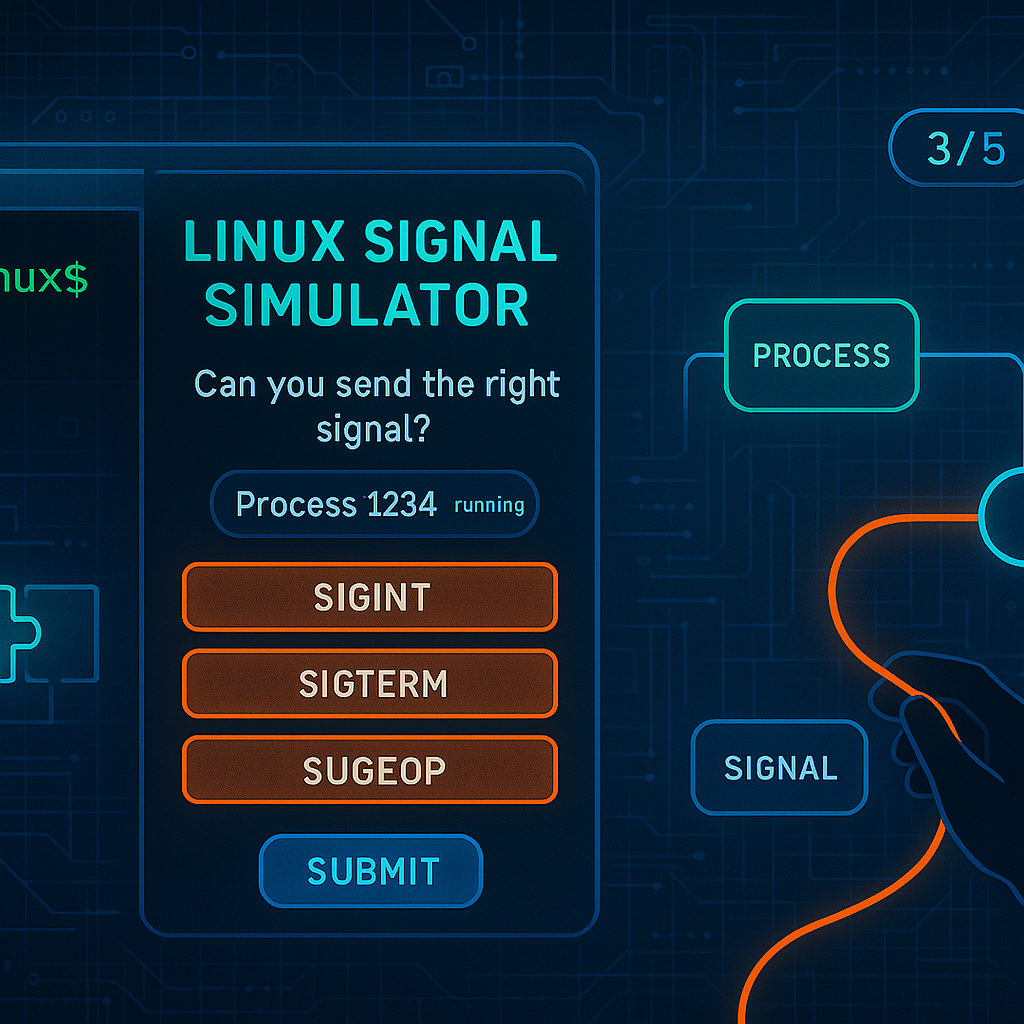
🚦 Linux Signal Simulator: Can You Send the Right Signal?
Send the right Linux signal in this interactive quiz for sysadmins and developers. Choose the…
🧭 Live System Resource Profiler – Simulate CPU/RAM/I/O Load in Real-Time
Visualize simulated system load through interactive CPU, RAM, and I/O meters using this browser-based animated…
Advanced Process Sandbox Simulator – Interactive Process Tree & Memory Visualizer
🧠 Simulate and visualize process operations in a fully offline, client-side drag-and-drop sandbox with memory…
How to Use the Password Policy Validator for Secure Credential Management
Learn how to use password-policy-validator to audit, validate, and harden password rules across your enterprise…